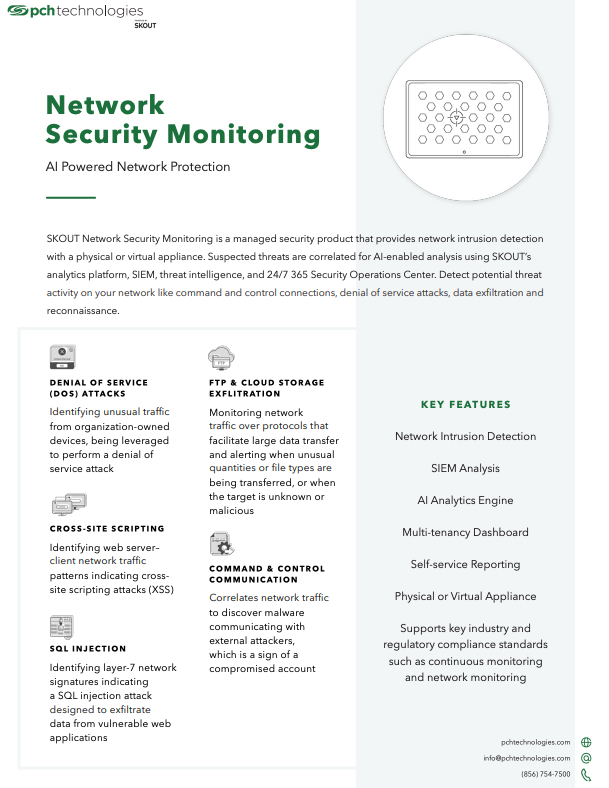
SKOUT Network Security Monitoring
SKOUT Network Security Monitoring is a managed security product that provides network intrusion detection with a physical or virtual appliance. Suspected threats are correlated for AI-enabled analysis using SKOUT’s analytics platform, SIEM, threat intelligence, and 24/7 365 Security Operations Center. Detect potential threat activity on your network like command and control connections, denial of service attacks, data exfiltration and reconnaissance.
The time to plan your approach to cybersecurity is now. PCH can help.

“SKOUT WFH Security Bundle”
Our solution brief goes over the best IT support
model for your business