SKOUT Office 365 Security Monitoring
SKOUT Office 365 Security Monitoring is a managed security product that monitors Office 365 activity using SKOUT’s analytics platform, SIEM, threat intelligence, and 24/7 365 Security Operations Center to identify threat-like behavior such as unauthorized access to cloud mailboxes, admin changes in the environment, impossible logins, and brute force attacks.
The time to plan your approach to cybersecurity is now. PCH can help.

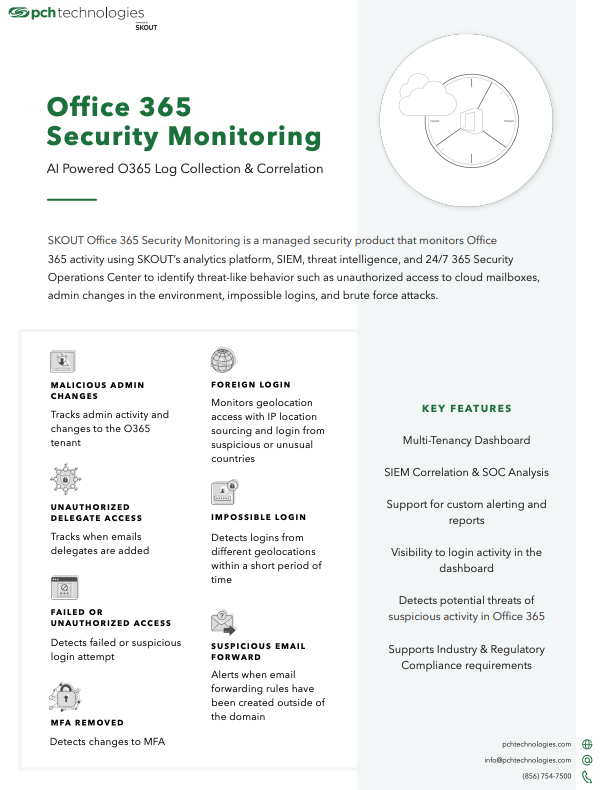
SKOUT Office 365 Security Monitoring
Our solution brief goes over the best IT support model for your business